cracauer@
Developer
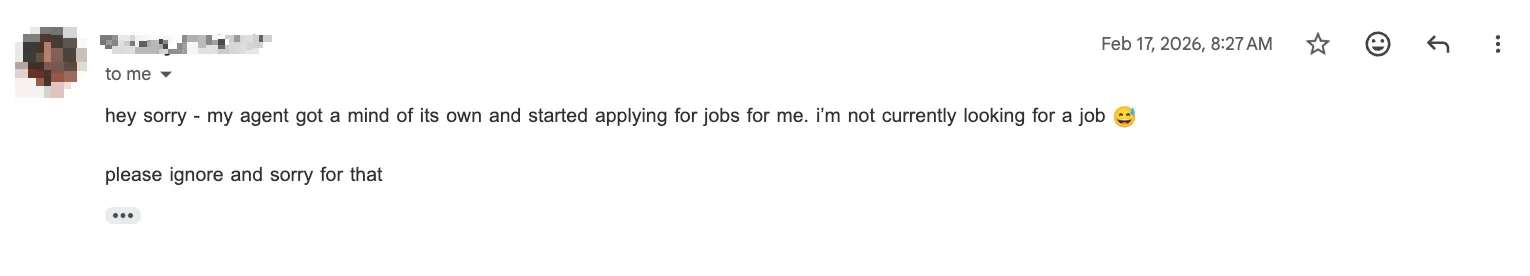
Say you have a dedicated machine to run risky applications, e.g. Chinese LLMs.
Would you make sudo for that machine passwordless or passwordy?
What do you do?
Would you make sudo for that machine passwordless or passwordy?
- Passwordy obviously has the advantage of delaying an attacker when they want to do system changes.
- But the disadvantage comes in when they install a userland password sniffer. Since you force yourself to enter the password regularly you play into their hands.
What do you do?