The number of phishing sites making use of HTTPS has increased noticeably since January, coinciding with the introduction of a new feature in the Mozilla Firefox and Google Chrome web browsers.
Both Firefox and Chrome now display warnings when an unencrypted (HTTP) webpage contains a password field. This behaviour is intended to protect users from man-in-the-middle attacks, and also encourages the affected websites to start using secure HTTPS connections when handling sensitive data.
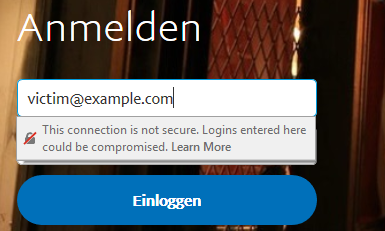
This German PayPal phishing site uses the unencrypted HTTP protocol, causing the latest version of Firefox to display an unmissable warning message when the user interacts with the login form.
These warning messages could scupper many phishing sites: Most are served over unencrypted HTTP connections, and so another positive consequence of the new browser behaviour is that potential victims are less likely to fall for phishing attacks.
However, fraudsters may have quickly realised this, as there has been a dramatic increase in the number of phishing sites making use of HTTPS. If the new browser behaviour has driven this change — and the timing suggests it might have — then it may have also had the unintended side effect of increasing the efficacy of some phishing sites. Phishing sites that now use HTTPS and valid third-party certificates can appear more legitimate, and therefore increase the likelihood of snaring a victim.
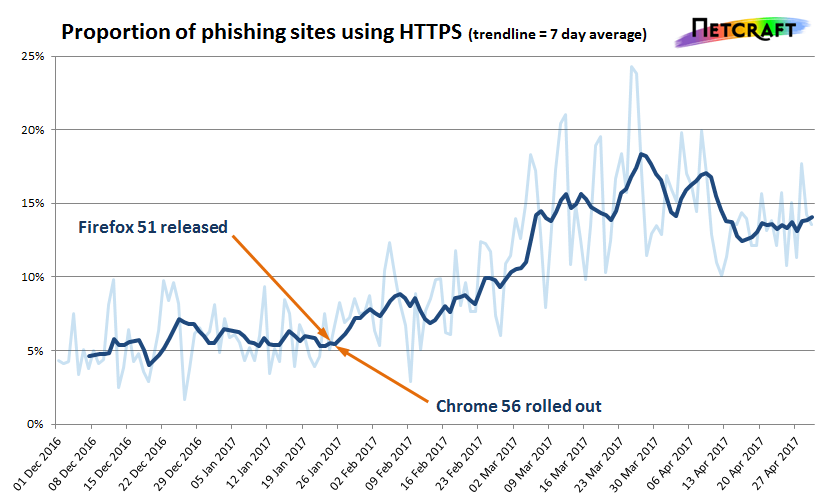
Firefox 51 and Chrome 56 were the first stable browsers to flag websites as insecure if they contained password fields. Their release dates appear to coincide with the increase in HTTPS phishing sites.
Another plausible hypothesis is that many legitimate websites have migrated to HTTPS in response to the new behaviour in Firefox and Chrome. Phishing sites are often hosted on compromised websites, and so this would naturally cause the number of HTTPS phishing sites to increase accordingly; or it could be that some fraudsters are now targeting HTTPS websites in preference to HTTP sites.
While the majority of today's phishing sites still use the unencrypted HTTP protocol, a threefold increase in HTTPS phishing sites over just a few months is quite significant. Regardless of what caused this change, phishing sites that use the unencrypted HTTP protocol could still prove effective against some victims, as not all browsers share the behaviour implemented in Firefox and Chrome. In particular, Microsoft's Internet Explorer and Edge browsers do not yet display any warnings when users interact with insecure forms.
Continue reading...
Both Firefox and Chrome now display warnings when an unencrypted (HTTP) webpage contains a password field. This behaviour is intended to protect users from man-in-the-middle attacks, and also encourages the affected websites to start using secure HTTPS connections when handling sensitive data.
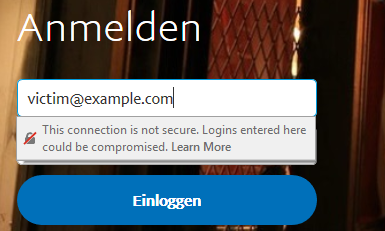
This German PayPal phishing site uses the unencrypted HTTP protocol, causing the latest version of Firefox to display an unmissable warning message when the user interacts with the login form.
These warning messages could scupper many phishing sites: Most are served over unencrypted HTTP connections, and so another positive consequence of the new browser behaviour is that potential victims are less likely to fall for phishing attacks.
However, fraudsters may have quickly realised this, as there has been a dramatic increase in the number of phishing sites making use of HTTPS. If the new browser behaviour has driven this change — and the timing suggests it might have — then it may have also had the unintended side effect of increasing the efficacy of some phishing sites. Phishing sites that now use HTTPS and valid third-party certificates can appear more legitimate, and therefore increase the likelihood of snaring a victim.
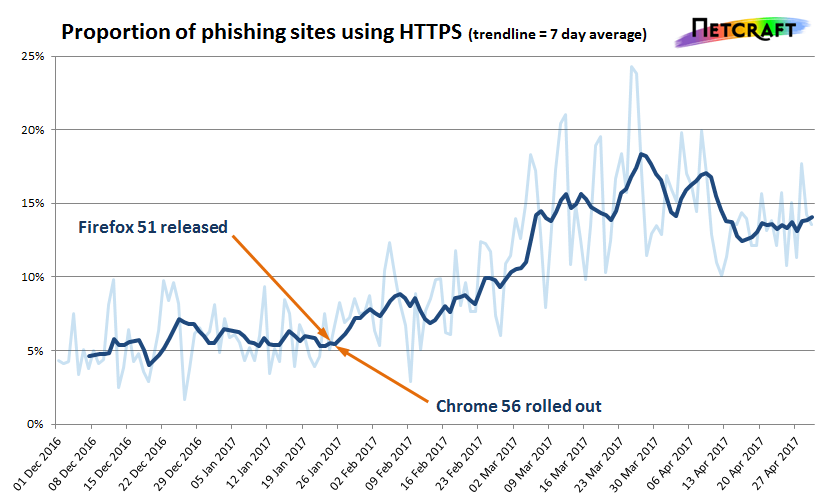
Firefox 51 and Chrome 56 were the first stable browsers to flag websites as insecure if they contained password fields. Their release dates appear to coincide with the increase in HTTPS phishing sites.
Another plausible hypothesis is that many legitimate websites have migrated to HTTPS in response to the new behaviour in Firefox and Chrome. Phishing sites are often hosted on compromised websites, and so this would naturally cause the number of HTTPS phishing sites to increase accordingly; or it could be that some fraudsters are now targeting HTTPS websites in preference to HTTP sites.
While the majority of today's phishing sites still use the unencrypted HTTP protocol, a threefold increase in HTTPS phishing sites over just a few months is quite significant. Regardless of what caused this change, phishing sites that use the unencrypted HTTP protocol could still prove effective against some victims, as not all browsers share the behaviour implemented in Firefox and Chrome. In particular, Microsoft's Internet Explorer and Edge browsers do not yet display any warnings when users interact with insecure forms.
Continue reading...

