I agree with
Zirias on this.
Part of blocking outgoing is simply information security. There are some protocols that broadcast stuff: Windows machines are particularly chatty and may leak information about your machines/network. If you look at a typical broadband connection like Cable Modem, it's a shared pipe and you can see your neighbors if you wanted.
Another part of blocking outgoing is simply "network hygine". Why send traffic out of your network that doesn't need to go out of it? Yes in theory upstream devices like routers should be blocking things but if you can do a little bit to lighten that load, why not? It also prevents your devices from being accused as part of a DDOS or other bad things.
It's convienent and easy to say "block in on WAN unless it matches an outgoing connection, allow everything in on LAN to go out WAN". That is the default stance of 99% of consumer devices, simply because it gives a good bit of security against unsolicited inbound and makes it easy for home users to "just work" out of the box.
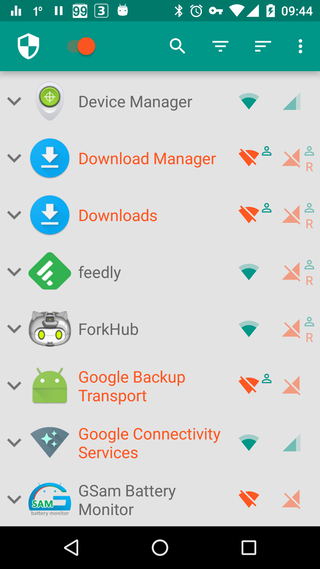
The strongest security stance for a firewall device starts out with "block in/out on all interfaces", and then you start specifically adding rules to allow desired traffic. That leads to this:
Blocking outgoing ports introduces unnecessary complications coz then the user need to know which app is using which port and then allow it in the firewall.
From a pure standpoint the statement is true, BUT it is your network and your devices so if you want to exercise that level of control, no one can tell you "You're wrong" with a straight face. All it means is that if some like say a spouse complains that "my application doesn't work" you need to stop what you are doing, investigate and add a few ports to the ruleset. Your call as to what is easier.
In the past I have done this on my home network which has my machines (FreeBSDs, Linux for work) and wife's/guest mostly Windows or iPhones. Surprisingly few outbound things are actually needed for normal operation. If it was a dozen TCP and a handful of UDP ports it was alot. That included normal things like DNS, NTP, HTTP/HTTPS etc.