D
Deleted member 9563
Guest
plug in some small device via usb into an untrusted OS
Pwnd! The USB code is untrusted too.
plug in some small device via usb into an untrusted OS
True but there's nothing stopping malware from exploiting ring 0 code and injecting itself there. Or simply ask for Administrator access and install itself that way. What I was trying to say is that once malware has its hooks (or should I say claws?) in the OS you simply cannot trust it anymore and any attempt to remove or detect it can be hooked or otherwise subverted.Amiga was quite different case because it had no memory management that would have kept user space programs and kernel memory space separate. In hindsight the design was just asking for trouble because it allowed any program to modify the OS internals as they wished.
… MS Windows that allows the user to perform very dangerous operations without any warnings if the system is set up that way (which is unfortunately more common than not).
Yeah but the modern malware has to first get around this privilege separation and that can be difficult or easy depending on the user and the system. On FreeBSD and most of the UNIX-like systems this is very hard because the users tend to be a bit more aware of the dangers of running unknown software and the systems are built with much more sense to enforce the restrictions than on let's say MS Windows that allows the user to perform very dangerous operations without any warnings if the system is set up that way (which is unfortunately more common than not).
Until the hypervisor itself gets infectedMaybe the OP should take a look at Qubes:
https://www.qubes-os.org/
It's kind of a bare-metal hypervisor. It isolates from the outside and you can run freeBSD, Windows or whatever on top of it.
That won't matter much. Remember CodeRed infecting IIS servers? That infected a machine and ran entirely from memory. It never dropped any files.SmartOS is a Type 1 hypervisor that doesn't install to disk; /etc is recreated on boot and you can't write under /usr.
Qubes is built on Xen which seems to regularly have vulnerabilities, some that garner a high risk rating by US CERT.
Besides, these virtualization products are all meant to utilize the large capacity of servers. Security was not the primary goal.
Don't bother with backdoors in OS, there's a known problem in hardware system.I do not like the idea of backdoors in my OS
Don't bother with backdoors in OS, there's a known problem in hardware system. . . .
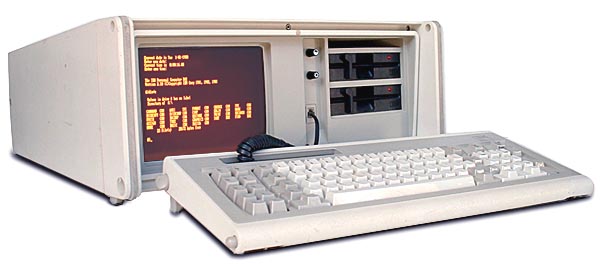
So start stockpiling old computers now in the hope that we can prolong the inevitable where we are all in digital (and probably physical) cages run by corporations and governments
Heh, no it means that you must be paranoid about both hardware *and* software.
So start stockpiling old computers now in the hope that we can prolong the inevitable where we are all in digital (and probably physical) cages run by corporations and governments
Imagine the looks I get when I show up to a starbucks with a X-31 or a T-43... and a stack of CDs and a sony discman, Good to hear! My girlfriend thinks I have a problem and gets quite annoyed when she trips over one of my stacks of old T23 Thinkpads... But she'll see! One day...
Imagine the looks I get when I show up to a starbucks with a X-31 or a T-43... and a stack of CDs and a sony discman
As far as software security goes, it's probably the most evolved system. It does require modern hardware and will not disable stuff like the Intel management engine in hardware.
I thought about giving that old HP-PA to someone, but for the same reasons you folks can't bin junk (her words, not mine), I can't either. And when there is discussion about a tax on them, you know you did something right.Heh, no it means that you must be paranoid about both hardware *and* software.
So start stockpiling old computers now in the hope that we can prolong the inevitable where we are all in digital (and probably physical) cages run by corporations and governments
