I read about Geli full disc encryption, but did not like that on boot you have to sit at the console to enter the disk password. I'd like to be able to restart my home server from work after a power failure.
I googled a lot and finally found this mailing list posting:
Edit: the first point of the quote is wrong, the encrypted system gets the kernel of the unencrypted system.
I wondered why I hadn't found more postings with the reboot -r pattern.
Anyway, I liked the idea, especially as the unencrypted first system is fully working and can send me an email that it needs attention and needs me to ssh in and enter the Geli password for the second system.
Of course, on booting the machine might be already sitting in burglar's home. But I could have a webcam pointing to the machine ..
Or burglar could have manipulated sshd of the first system to log my password. But, he could also manipulate the keyboard, or the keyboard driver of the boot loader, so entering the password directly in the computer does not help.
So I wanted to try this out, set up a Virtualbox and ran the FreeBSD installer.
Actually, the idea was rather easy to set up.
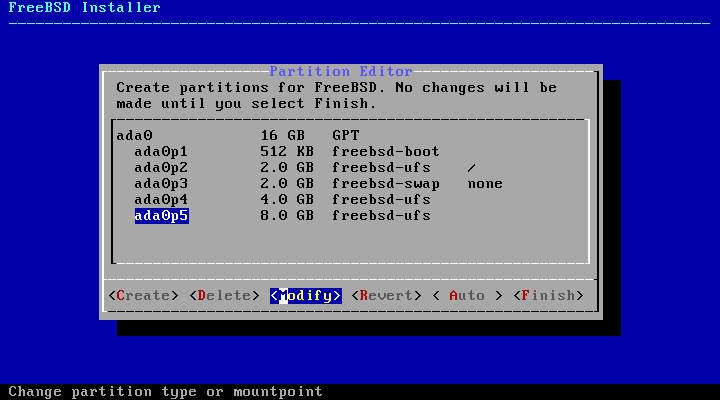
From the installer UI partitioned the disk, no mount point for the Geli partitions.
Geli inited 4 and 5:
mounted it:
copied the root file system:
It actually booted into ada0p4.eli but complained about /dev
So I rebooted, mounted and mkdir'ed /dev and /proc
Also renamed the second machine to geli in its rc.conf
Next time it worked!!
geliboot still prompted for the password, and would not continue booting until I entered it. I guess I should have left the -b option.
So I removed geli from loader.conf, no more password prompt, but have to do things by hand:
Added swap:
I googled a lot and finally found this mailing list posting:
- There is an unencrypted FreeBSD (caveat: kernel must match that of the encrypted system, care when upgrading)
- System boots into that unencrypted FreeBSD
- I access that unencrypted system over SSH
- Encrypted system is unlocked
- reboot -r is used to boot into that system (man reboot explains that quite well)
Edit: the first point of the quote is wrong, the encrypted system gets the kernel of the unencrypted system.
I wondered why I hadn't found more postings with the reboot -r pattern.
Anyway, I liked the idea, especially as the unencrypted first system is fully working and can send me an email that it needs attention and needs me to ssh in and enter the Geli password for the second system.
Of course, on booting the machine might be already sitting in burglar's home. But I could have a webcam pointing to the machine ..
Or burglar could have manipulated sshd of the first system to log my password. But, he could also manipulate the keyboard, or the keyboard driver of the boot loader, so entering the password directly in the computer does not help.
So I wanted to try this out, set up a Virtualbox and ran the FreeBSD installer.
Actually, the idea was rather easy to set up.
From the installer UI partitioned the disk, no mount point for the Geli partitions.
Code:
root@geliboot:~ # gpart show
=> 40 33554352 ada0 GPT (16G)
40 1024 1 freebsd-boot (512K)
1064 4194304 2 freebsd-ufs (2.0G)
4195368 4194304 3 freebsd-swap (2.0G)
8389672 8388608 4 freebsd-ufs (4.0G)
16778280 16775168 5 freebsd-ufs (8.0G)
33553448 944 - free - (472K)
root@geliboot:~ # df -h
Filesystem Size Used Avail Capacity Mounted on
/dev/ada0p2 1.9G 1.3G 537M 71% /
devfs 1.0K 1.0K 0B 100% /devGeli inited 4 and 5:
Code:
root@geliboot:~ # geli init -b -e AES-XTS -l 256 -s 4096 /dev/ada0p4
root@geliboot:~ # geli attach /dev/ada0p4
root@geliboot:~ # geli status
Name Status Components
ada0p4.eli ACTIVE ada0p4
ada0p5.eli ACTIVE ada0p5
root@geliboot:~ # newfs -t -U -L rootfs /dev/ada0p4.elimounted it:
Code:
root@geliboot:~ # mkdir /mnt/ada0p4.eli
root@geliboot:~ # mount /dev/ada0p4.eli /mnt/ada0p4.eli/copied the root file system:
Code:
root@geliboot:~ # rsync -av --exclude="lost+found" --exclude="mnt" --exclude="proc" --exclude="dev" / /mnt/ada0p4.eli/
root@geliboot:~ # kenv "vfs.root.mountfrom=ufs:/dev/ada0p4.eli"
vfs.root.mountfrom="ufs:/dev/ada0p4.eli"
root@geliboot:~ # reboot -rSo I rebooted, mounted and mkdir'ed /dev and /proc
Also renamed the second machine to geli in its rc.conf
Next time it worked!!
geliboot still prompted for the password, and would not continue booting until I entered it. I guess I should have left the -b option.
So I removed geli from loader.conf, no more password prompt, but have to do things by hand:
Code:
root@geliboot:~ # geli load
root@geliboot:~ # geli attach /dev/ada0p4Added swap:
Code:
root@geliboot:~ # geli onetime -d -e 3des ada0p3
root@geli:~ # cat /etc/fstab
# Device Mountpoint FStype Options Dump Pass#
#/dev/ada0p2 / ufs rw 1 1
#/dev/ada0p3 none swap sw 0 0
/dev/ada0p5.eli /data ufs rw 1 1
/dev/ada0p3.eli none swap sw 0 0
root@geli:~ # swapinfo
Device 1K-blocks Used Avail Capacity
/dev/ada0p3.eli 2097152 0 2097152 0%
