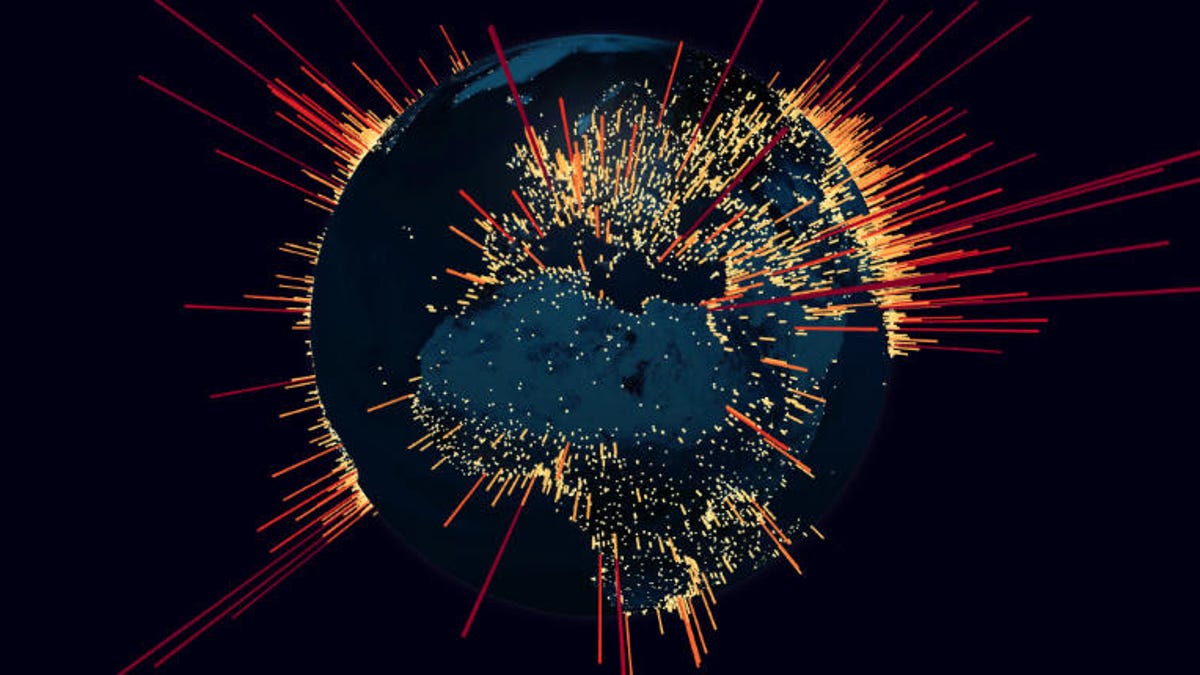
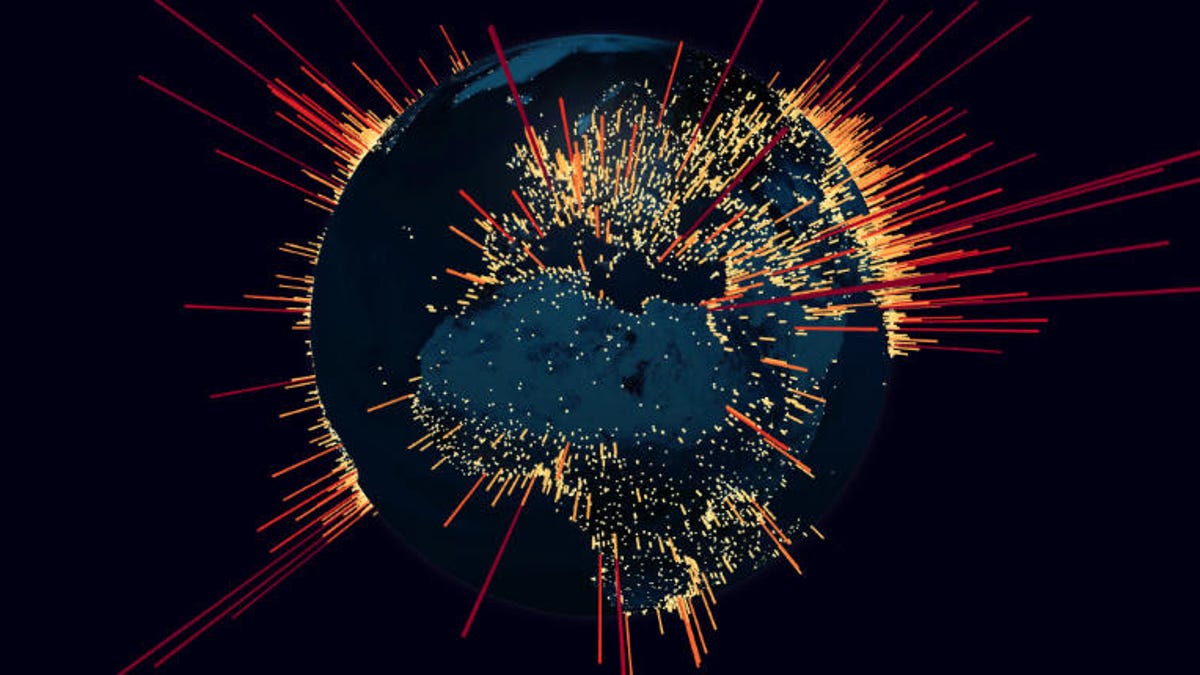
China wants to introduce a "new ip protocol" that includes potentially a kill switch. I don't see how it'll happen, I mean IPV6 still hasn't fully been implemented everywhere.
Yes, China (and Russia and a few other totalitarian states) want to have the ability to perform censorship and espionage at the protocol level. That has been making the round for months now. And in view of their political stance, this is completely not surprising. There is a reason that one shouldn't buy networking gear from Huawei. By the way, many other governments also like to perform espionage, all I need to say is Clipper chip. The difference is that the Chinese government and its commercial arm Huawei are totally open about it: We want the low-level protocols to be make censorship easier, and if the IETF doesn't give it to us, we'll go somewhere else. They're not the slightest bit ashamed of being a totalitarian regime, nor do they have to be.
And: IPv6 is pretty universally installed. I've seen quite a few IPv6-only installation.
Can anybody that's been around longer then I have please tell me if anything similar to this, has changed the Internet before?
It has undergone many changes. Not at the basic protocol level so much, but in questions of governance, commercialization, and such. Example is the sale of the .us domain; the move of the root servers. A lot was brought on by the fact that the IANA died; it is at times like this that I think how much we all miss Jon Postel. Alas, he couldn't have stopped the flow of money and power by himself; today the internet is the most important industry in the world (more than oil or transportation), so it is not surprising that it also has to respond to political and economic pressure.
They may implement that for their own country but not for the rest of the world. Too much commerce depends on the Internet to just cut it off.
Two comments. Russia and China could easily legislate that the internet within their countries only use protocols that are allowable to them. Then they could route content from the outside. That's exactly what the great firewall does today; all you'd be adding would be a protocol translation.
The idea of central authorities doesn't quite sit right with me. Sure we have "free" and anonymous ones like LetsEncrypt (for now) but surely a more SSH approach could have been taken.
I am pretty sure in the early days it was just a way of linking a hosts bank account (to pay for the certificate) with the certificate to provide some tracability.
No, not really. There are two things that are being conflated here. First, we need SSL (meaning https) to security in transit, so packets don't get spied on or modified along the way. In the normal encryption scheme we use today, that means we need keys. SSH also uses keys. Ever noticed that when you first ssh to a host, it asks you whether you want to trust that host? That's because of the second function of https: authentication. When I look at the web site www·ibm·com, I want to be 100% sure that I'm looking at the real thing (the web site of Itsy Bitsy Machines, a local chainsaw repair place that my son and me operate out of our basement), and not some impostor like Irish Business Machines or Immense Bowel Movement. So when a certificate authoritity issues a SSL certificate to my son and me, they really need to check that (a) we hold the trademark or copyright on the term "IBM", (b) we really are authorized representatives of Itsy Bitsy Machines. That probably requires my passport, matching my picture against what I look like, a certified copy of the articles of incorporation of IBM, Inc., a statement signed in ink by the lawyer that this really is a truthful copy and that User RalphBSz with Elbonian passport number 12345 is indeed the chairman of the board of IBM. To really authenticate, you need a "web of trust", and that trust has to go back to entities such as courts and professions such as lawyers (please don't laugh now, you might cough and catch a virus). Today's certificate issuance doesn't do all of it, but it tries to get as close as practical (which isn't very).
Authentication is exactly the opposite of anonymity: To get an SSL certificate that demonstrates that this packet you got from server
www.ibm.com is really an expression of my son's and my opinion, the two of us can not possibly be anonymous, on the contrary: to verify that the web of trust isn't lying, you need to be able to go to the local courthouse and demand to inspect the paperwork for our company, and there you will see a photocopy of the same ugly picture of me, holding my trusty chainsaw.
Now, you say that there should also be a way to have anonymous but authenticated and encryption web service. For example, you might want to publish your opinions on the best way to tune up string trimmer engines on the web, but because you fear retaliation from me, you don't want to who kpedersen really is. I respect that, and being a champion of free speech, I'm also in favor of you being able to post your opinions (whether right or wrong is irrelevant) anonymously. But you need authentication: If someone comes back a week later to recheck your revolutionary carburetor adjustment instructions, you need to ensure that they really see your page; not a harmless looking page of bambi munching the flowers on a mountain meadow, which the most evil government of Elbonia has placed their after silencing you (silencer is a pun ... 2-stroke engines do have mufflers). Alas, today's https protocol and certificate issuance mechanism isn't designed to provide for anonymous but authenticated secure communications. Diffie and Hellman were not present in the room when it was designed. You lose.
But the important thing is this: Authentication is vitally necessary for 99% of all internet traffic, and I'm super happy that it is in widespread use now. Even though I had to spend countless evenings setting up the SSL certificates for my own personal stuff (even with LetsEncrypt it was painful).
And if you think, just for a moment, that real anonymity exists, you need to get a clue. With relatively little effort, an adversary can trace back where and who you are.
Anything that I cannot control makes failure possible and security impossible.
That is a common view in ultra-libertarian circles: Trust nothing, except oneself. Doesn't work and leads to complete nonsense. Very few people have the skills and knowledge to design and implement secure systems. Matter-of-fact, with today's complexity, I bet no single person can do it at all, and it requires teams. If you try to secure your own systems (or if I did), the result would be a security hole the size of a barn door. The reality is that you have to make informed decisions about what you can trust and what you can't.
Here's my favorite funny story about anonymity. A few years ago, I was running a political campaign in a local election, for a certain local issue that involved our schools. We were the "Yes on X" campaign, and measure X was something that was nearly universally popular in our local district, and eventually proposition X won at the election with 85% yes at over 55% turnout. But to make sure we would really win, we campaigned for it, we put up posters, we mailed out letters and postcards, and called voters. And we did that all very officially, with a campaign finance registration, keeping track of all donations and expenses, and all that.
Well, like all political issues, we had opponents. Let's call them Adam, Bob and Charlie. They wanted to campaign against measure X, but they knew that the community opinion was going to be overwhelmingly against them. To protect themselves, they wanted to campaign anonymously. So they sent a letter to the state campaign law and finance commission, asking whether it would be legal for them to anonymously put up posters saying "vote NO on X". The commission sent them a very nice letter, telling them that it is indeed legal to campaign anonymously and without disclosing where the money comes from, but only within very narrow limits (I think it was something like 20 posters, 200 letters and $2000 in expenditures). What these idiots forgot is that government is by its nature public: The campaign commission listed their case on the agenda of a public meeting, they discussed the case at the meeting (with journalists in attendance, although this question was so small it didn't get into the newspaper), and the letters were duly published in the record of the campaign's decision making on the web. Where I promptly found them. So when the posters "No on X" showed up by the road side (without any note on them: "paid for by campaign number 54321"), we immediately knew who had done it: Adam, Bob and Charlie. What's even funnier is that many of our volunteers had seen the three of them, driving around in a burgundy-colored Volvo station wagon, and putting up posters at street corners. What do we learn from this? If you want to do something anonymously, then (a) don't officially ask for permission from a public agency, and (b) don't wear your own faces and drive your own car when doing something anonymous on a public road.
 www.zdnet.com
www.zdnet.com
 www.zdnet.com
www.zdnet.com


